A transparent record of every USDT exchange, the USDT Transaction Explorer provides intelligence into the world of Tether. Whether you're a seasoned copyright analyst or just starting your journey, this tool empowers you to monitor transactions in real-time, gaining valuable awareness about activity dynamics. With its user-friendly interface and powerful tools, the USDT Transaction Explorer is an invaluable resource for anyone involved in the Tether ecosystem.
- Investigate transaction logs
- Find senders and destinations
- Gain current data on USDT flow
Unmasking Your IP
In the digital realm, your internet protocol address acts as a unique fingerprint, revealing your location and online activity. This comprehensive analysis delves into the methods used to detect your IP address, exploring its implications for privacy and security. We'll reveal common techniques employed by websites, applications, and even hackers to obtain this sensitive information.
Understanding how your IP address is leveraged is crucial for defending your online presence. Whether you're concerned about targeted advertising, data breaches, or simply maintaining your anonymity, this analysis will empower you to make informed decisions about your digital footprint.
- Common IP Address Detection Techniques
- Understanding IP Address Logging
- Protecting Your Privacy Online
Expose Hidden Identities and Network Locations
In the vast digital landscape, anonymity can be both a blessing and a curse. While it offers protection for individuals seeking privacy, it can also be exploited by malicious actors to mask their true identities and perform harmful activities. This is where a Proxy IP Hunter comes in handy. A powerful tool designed to discover the veil of anonymity, it allows you to identify the real IP addresses associated with proxy servers and locate the geographical location of users attempting to mask their presence online.
- Leveraging advanced scanning algorithms, Proxy IP Hunters can effectively sift through vast amounts of data to uncover hidden connections and identify potential threats.
- Whether you're a security professional combatting cybercrime, a researcher investigating online behavior, or simply someone afraid about your own privacy, a Proxy IP Hunter can provide invaluable insights into the complex world of online anonymity.
Your AI SEO Guide
In the dynamic landscape of search engine optimization (SEO), staying ahead of the curve requires constant evolution and adaptation. Introducing an innovative solution: the AI SEO Navigator. This cutting-edge tool leverages the power of artificial intelligence to revolutionize your SEO strategy, providing invaluable insights and guidance to maximize your online visibility.
- This groundbreaking tool
- analyzes your website and content
- highlighting areas for enhancement
- It generates data-driven recommendations to boost your SEO performance.
From keyword research and content creation to technical SEO audits, the AI SEO Navigator serves as website your dedicated SEO partner, assisting you navigate the complexities of search engine algorithms and secure lasting success.
Track USDT Transactions With Ease Quickly
In the dynamic world of copyright, staying ahead of the curve demands vigilance. USDT, a leading stablecoin, plays a pivotal role in facilitating rapid transactions. To navigate this landscape seamlessly, robust tools for detecting and analyzing USDT activities are indispensable. Fortunately, cutting-edge platforms now offer intuitive solutions to empower you with real-time insights into the USDT market. These tools provide comprehensive data visualization, enabling you to pinpoint trends, anomalies, and potential risks. By leveraging these capabilities, you can optimize your trading strategies with confidence.
- Advantages of Leveraging USDT Transaction Analysis Tools:
- Improved Market Understanding
- Risk Management
- Trading Optimization
Unveiling the Ultimate Guide to Proxy IP Research and Discovery
Venturing into the realm of anonymous internet access often necessitates a deep knowledge of proxy IP addresses. These virtual gateways grant an extra layer of protection, allowing you to browse the web with discretion. But how do you explore the complex world of proxy IPs? This comprehensive resource will empower you with the essential tools and strategies to effectively research and discover the best proxies for your needs.
Leveraging advanced discovery tools, understanding different proxy types, and evaluating their trustworthiness are just a few of the vital aspects covered in this ultimate guide.
- Furthermore, we'll delve into the details of proxy protocols and expose strategies for verifying your security.
- Prepare yourself to master the art of proxy IP research and discovery with this vital resource.
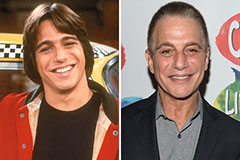 Tony Danza Then & Now!
Tony Danza Then & Now! Gia Lopez Then & Now!
Gia Lopez Then & Now! Monica Lewinsky Then & Now!
Monica Lewinsky Then & Now! Melissa Sue Anderson Then & Now!
Melissa Sue Anderson Then & Now! Mary Beth McDonough Then & Now!
Mary Beth McDonough Then & Now!